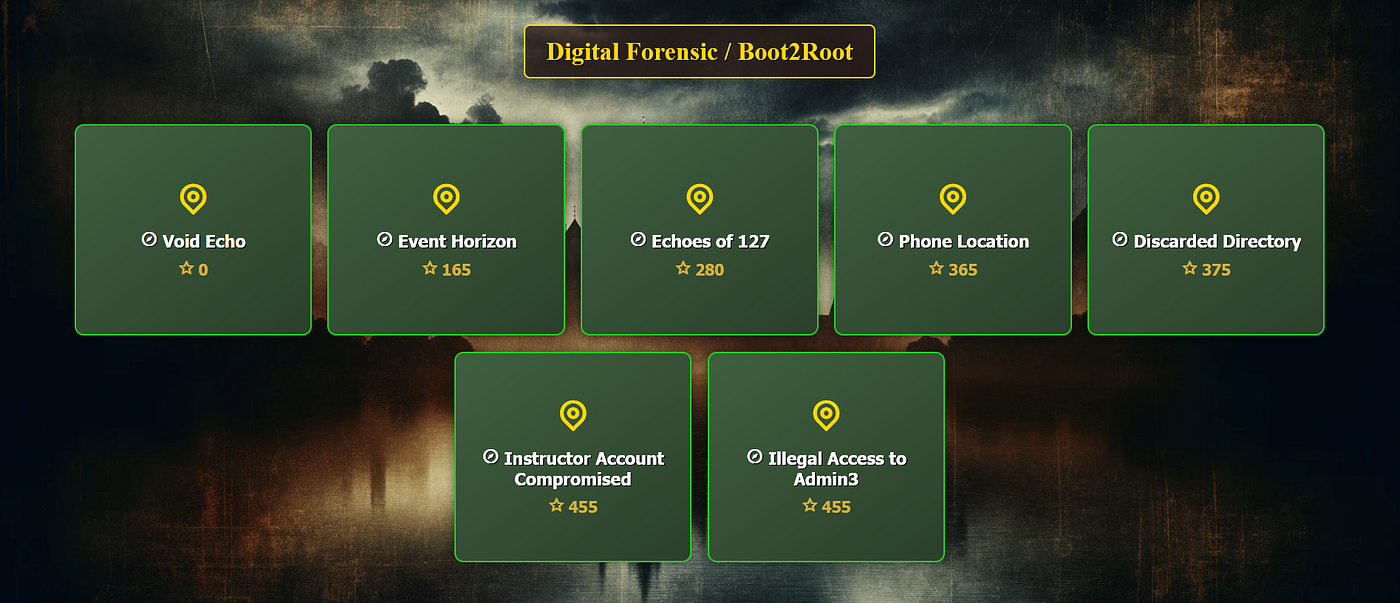
All seven forensics tasks in Knight CTF 2026 were chained, so each solution unlocked the next one. This writeup keeps the full investigation flow while presenting the steps in a cleaner format.
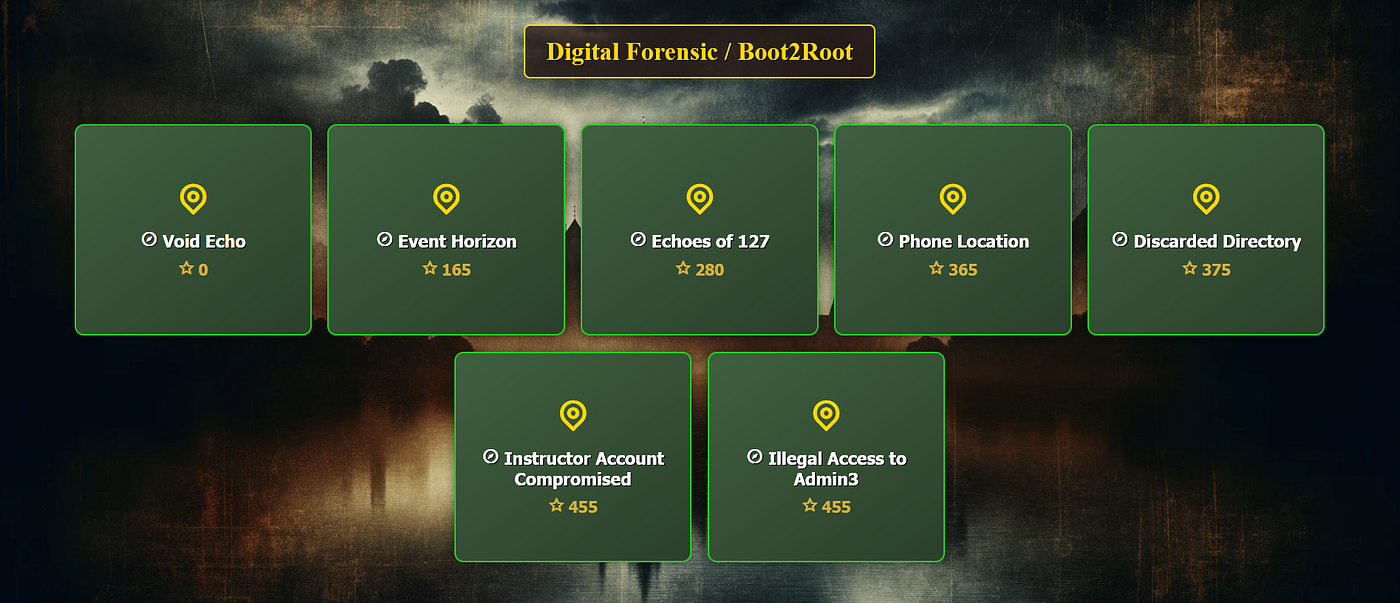
Challenge 1 - Void Echo
This first challenge mainly tested attention to the long scenario text. The provided list of user passwords contained the direct answer.
- Required clue: User3 password from the prompt
- Extracted value:
ksacademy3321
Flag: ksacademy3321
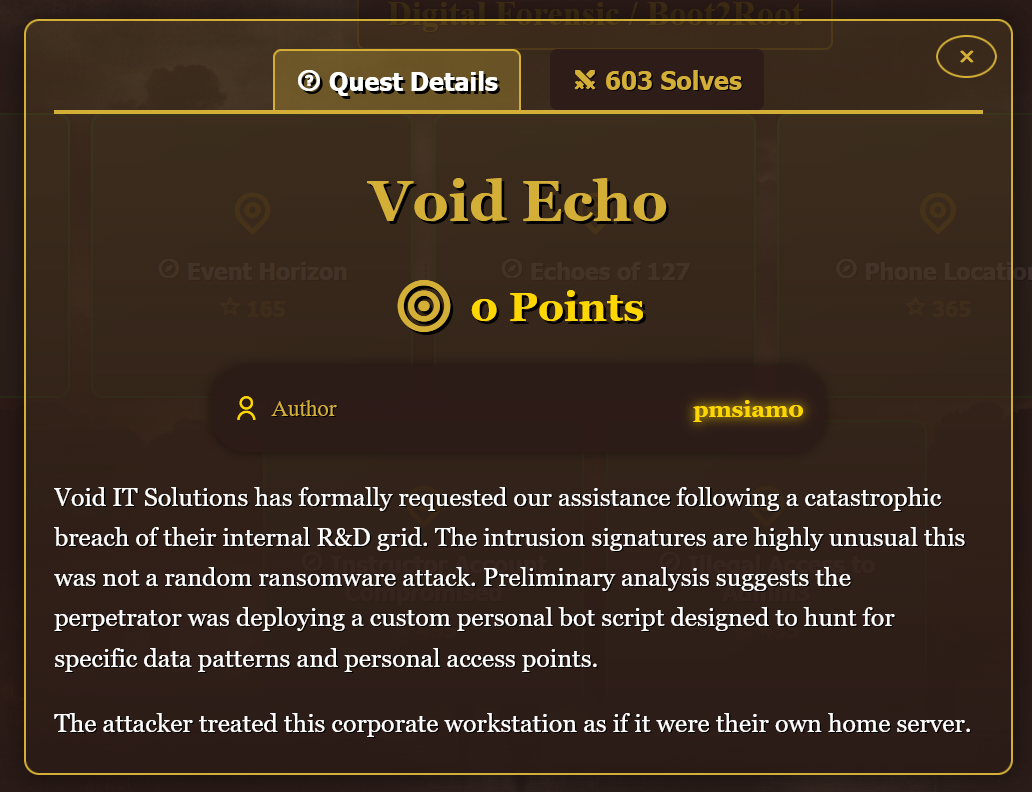
Challenge 2 - Event Horizon

I merged the split image parts, extracted the Windows VM disk, then opened the data in Autopsy.
During triage, I found a Telegram bot reference and used the narrative hints to identify the attacker username.
Then I parsed the SOFTWARE hive from:
/Windows/System32/config/SOFTWARE
and recovered the support token.
- Username:
Robert - Token:
_Establishes_Persistence
Flag: KCTF{Robert_Establishes_Persistence}
Challenge 3 - Echoes of 127
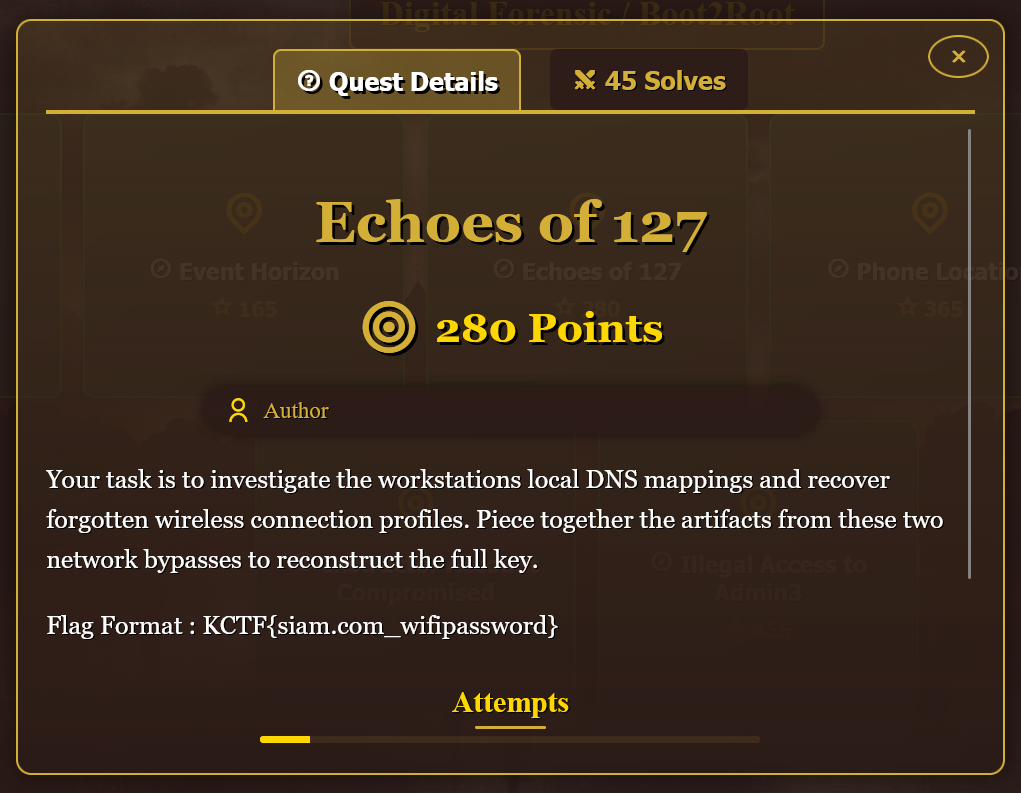
This challenge required combining host mapping evidence with a hidden Wi-Fi credential.
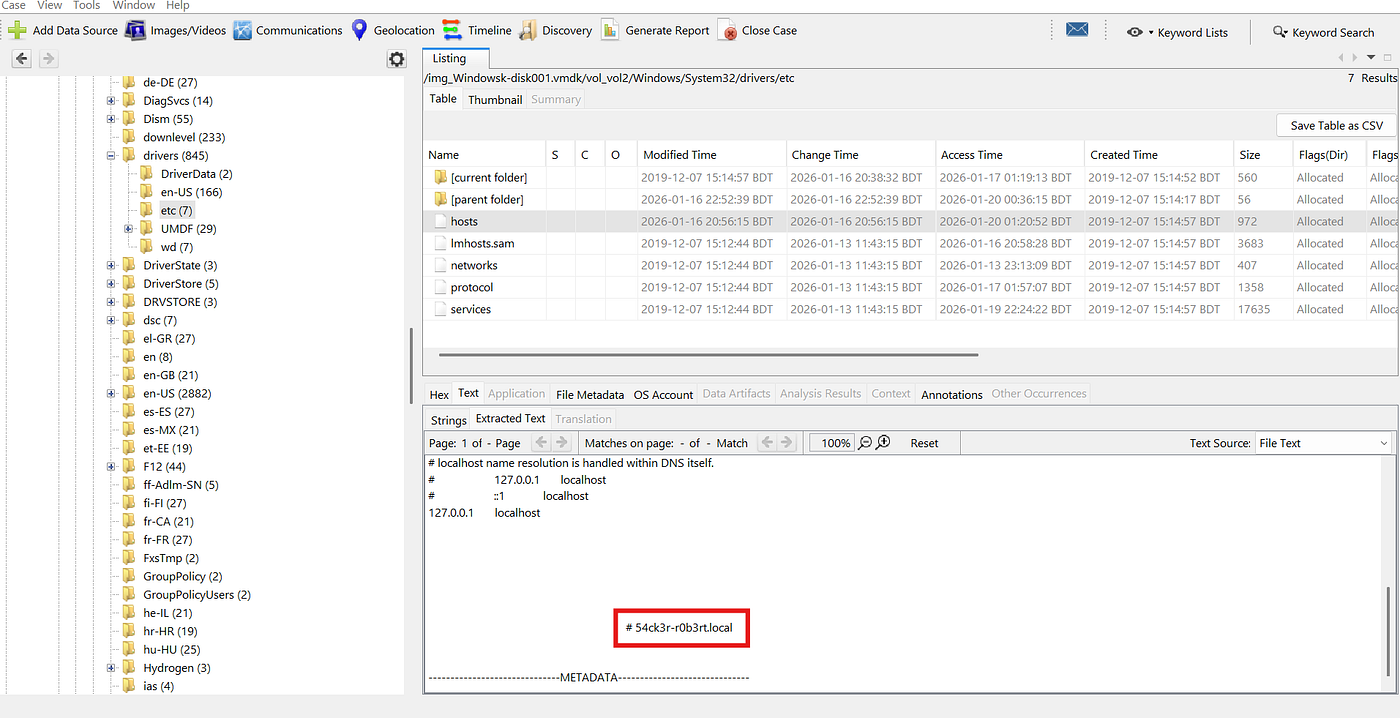
From local DNS mapping:
C:\Windows\System32\drivers\etc\hosts
I extracted:
- Host mapping key:
54ck3r-r0b3rt.local
Then I followed a clue file chain (ReadMe.txt -> alternate stream note) and recovered:
- Wi-Fi password:
Il0vesomeone1337
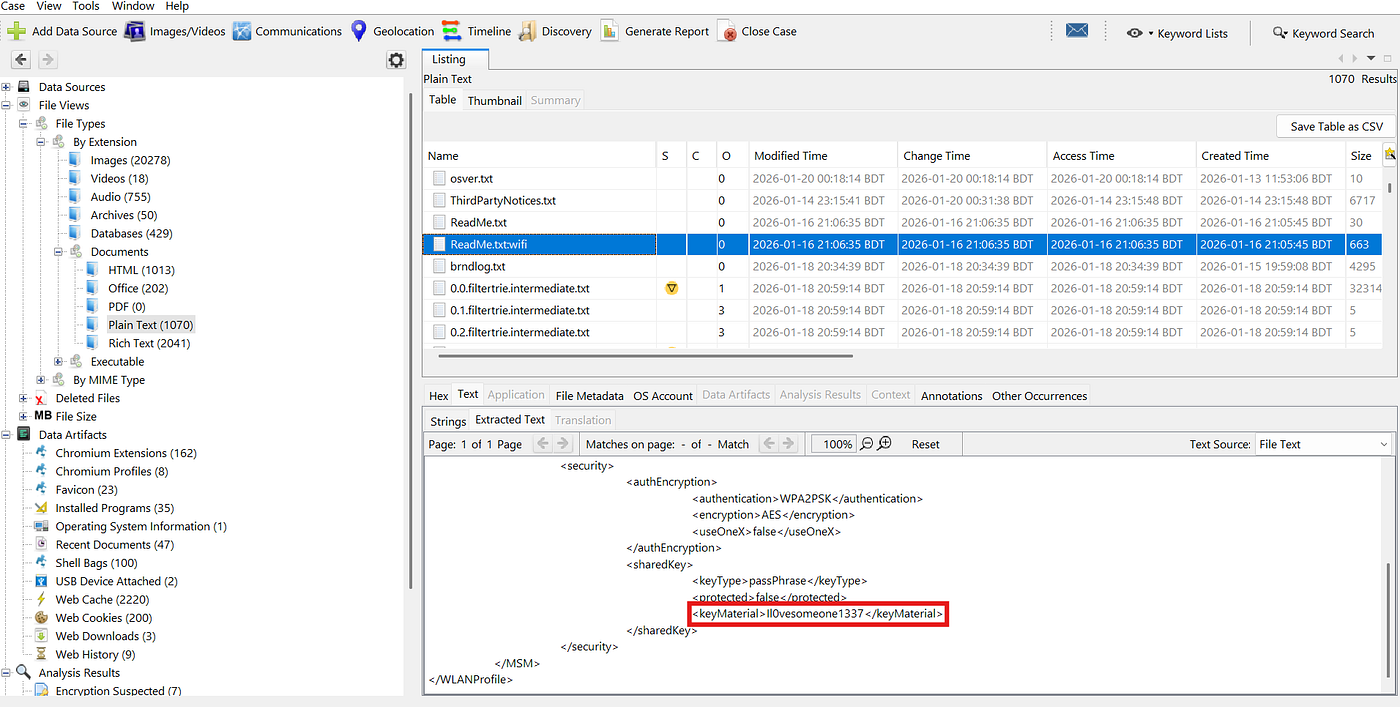
Flag: KCTF{54ck3r-r0b3rt.local_Il0vesomeone1337}
Challenge 4 - Phone Location
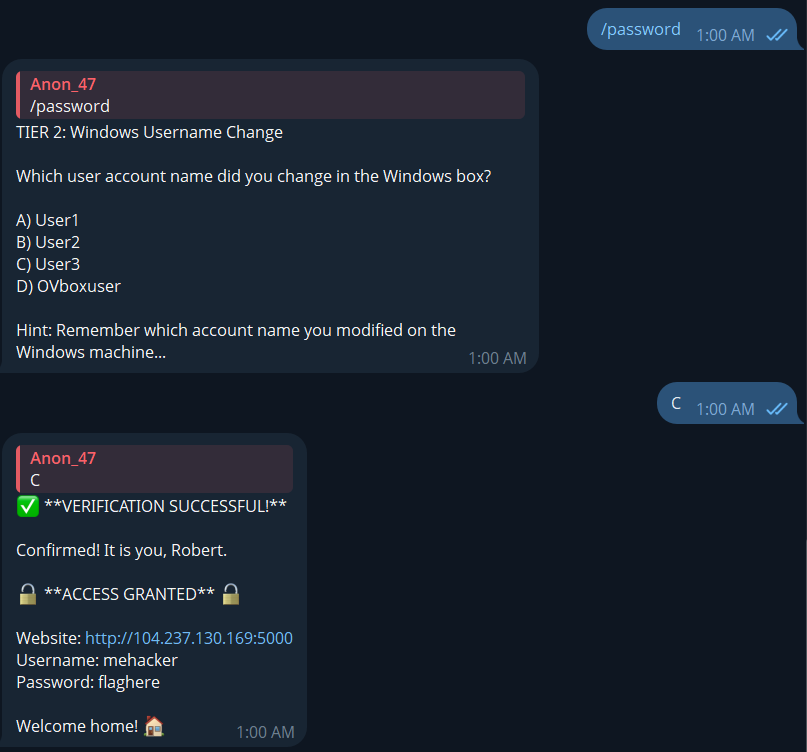
From the Telegram bot path, I reached the attacker’s home-lab panel and recovered the phone number.
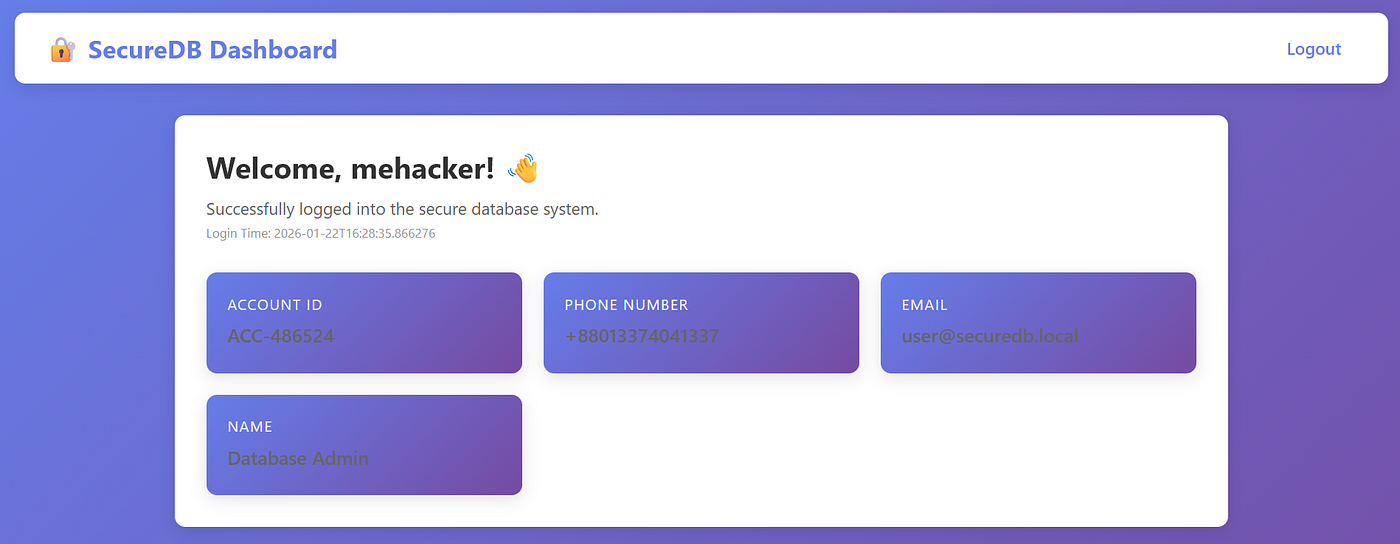
The IP was not obvious in the visible UI. Inspecting source comments revealed an API route for login history.
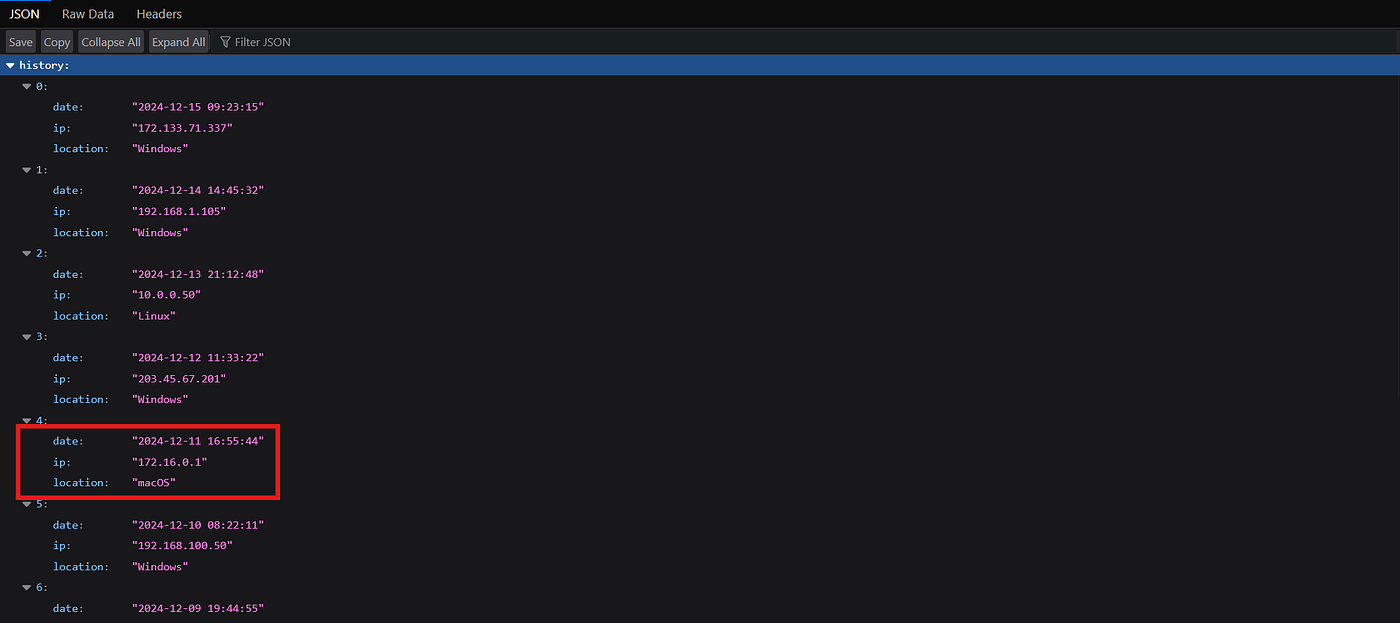
From that endpoint, I got last used macOS IP.
- Phone:
+88013374041337 - Last macOS IP:
172.16.0.1
Flag: KCTF{+88013374041337_172.16.0.1}
Challenge 5 - Discarded Directory

The wording hinted at deleted artifacts, so I started with recycle-bin style remnants.
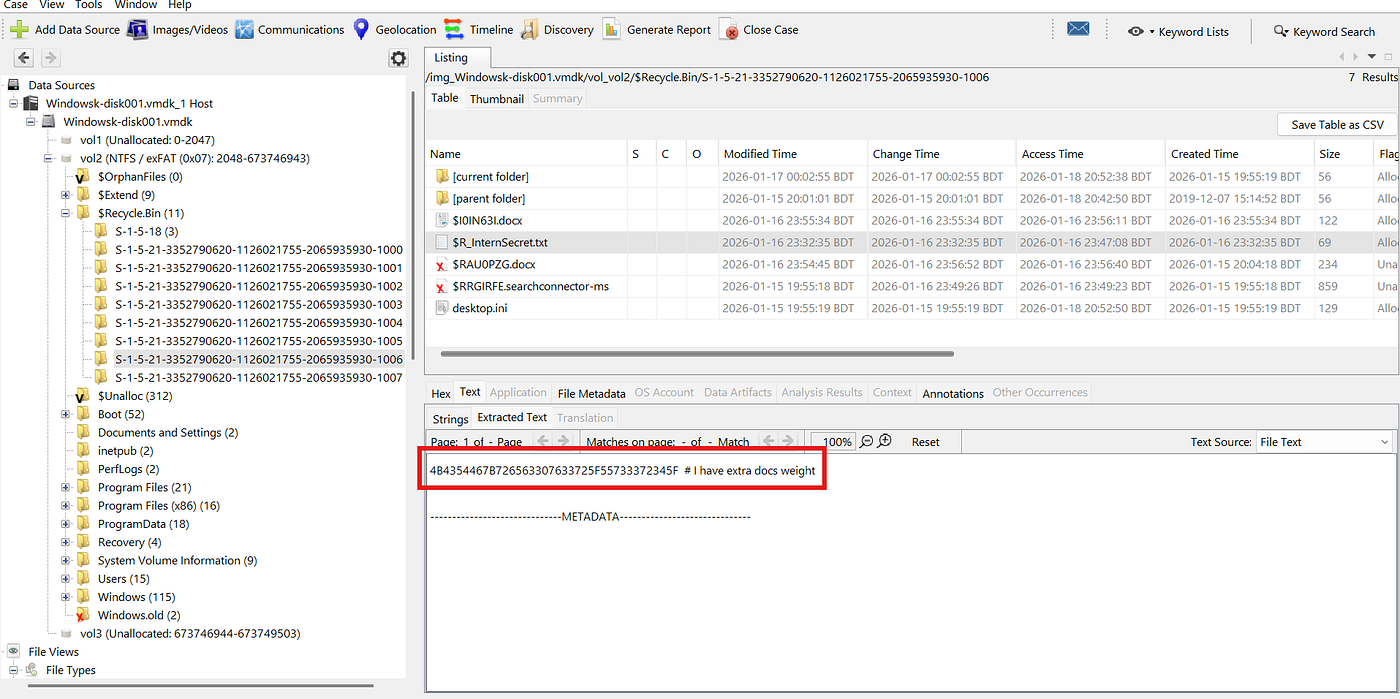
Hex from the recovered file decoded to partial flag text:
4B4354467B726563307633725F55733372345F -> KCTF{rec0v3r_Us3r4_
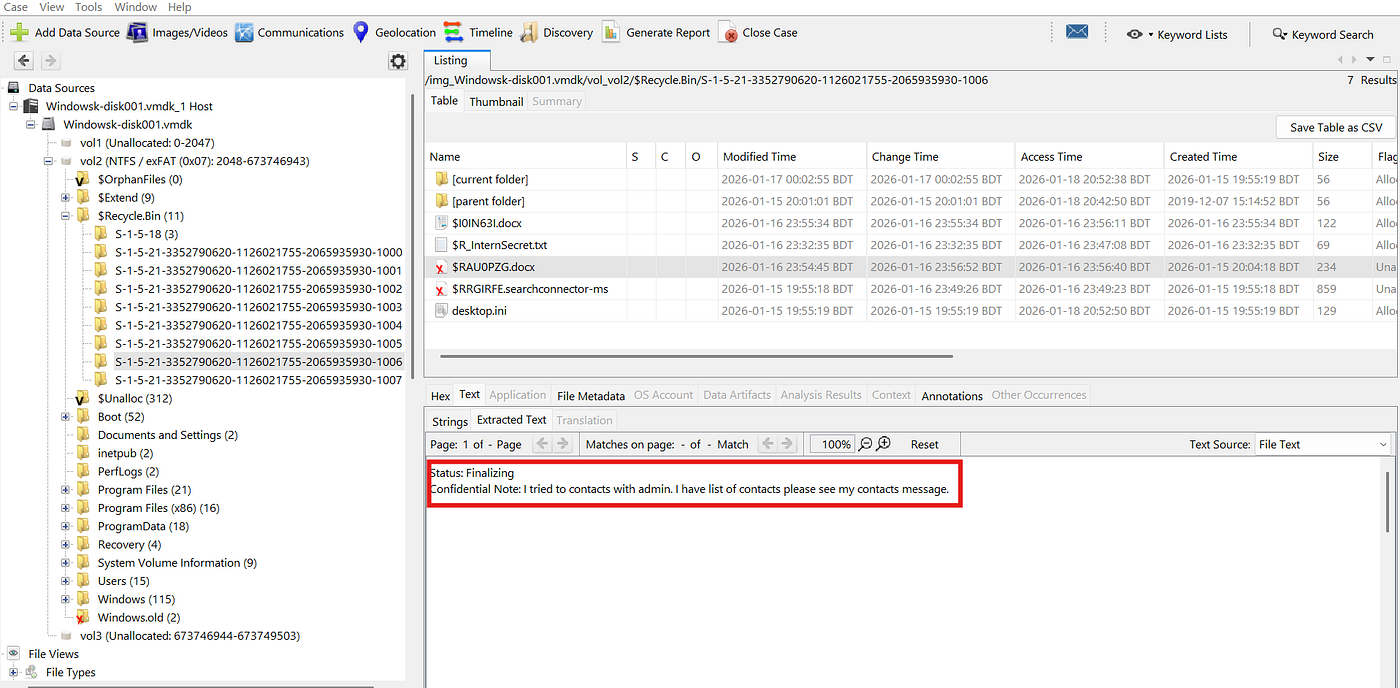
The second half came from Users/User4/Contacts (contact notes field).
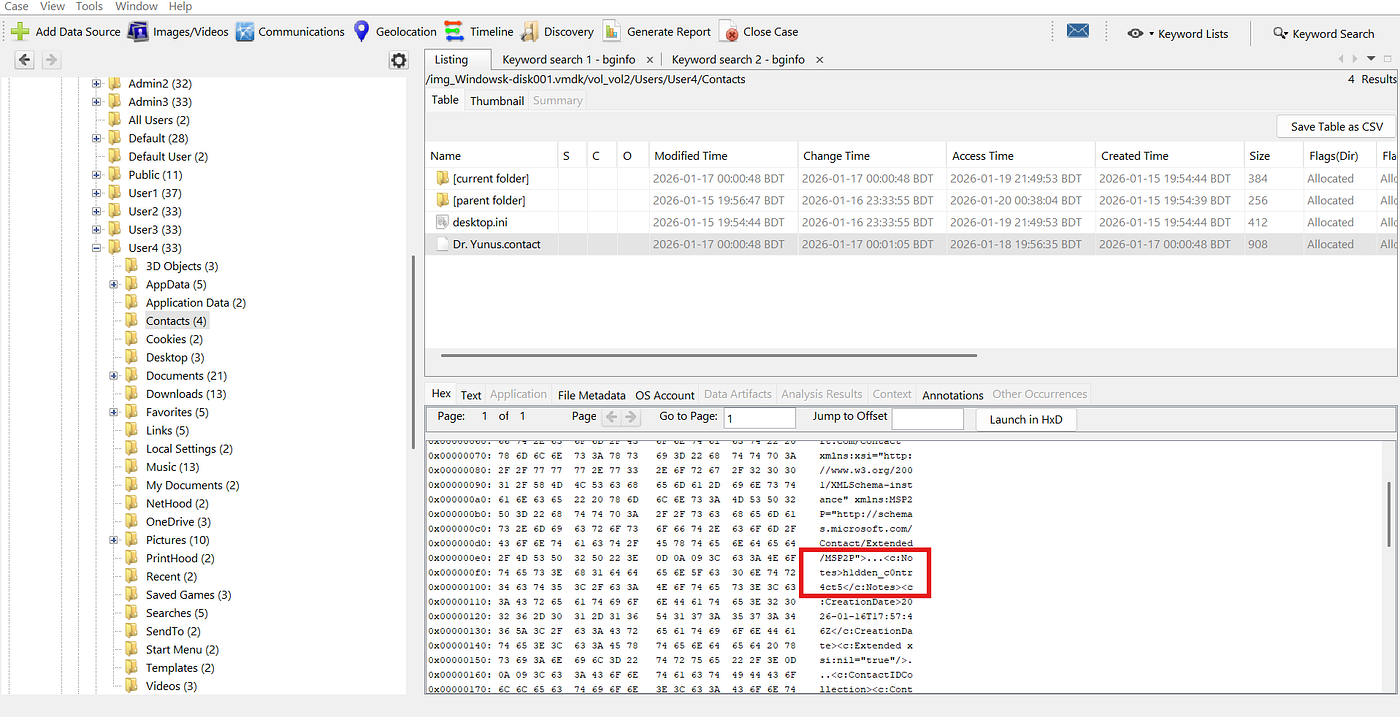
<c:Notes>h1dden_c0ntr4ct5</c:Notes>Flag: KCTF{rec0v3r_Us3r4_h1dden_c0ntr4ct5}
Challenge 6 - Instructor Account Compromised

The prompt linked admin2 to user5 and web development traces. I focused on browser local data under User5.
Path investigated:
C:\Users\User5\AppData\Local\Microsoft\Edge\User Data\Default\Local Storage\leveldb\000003.log
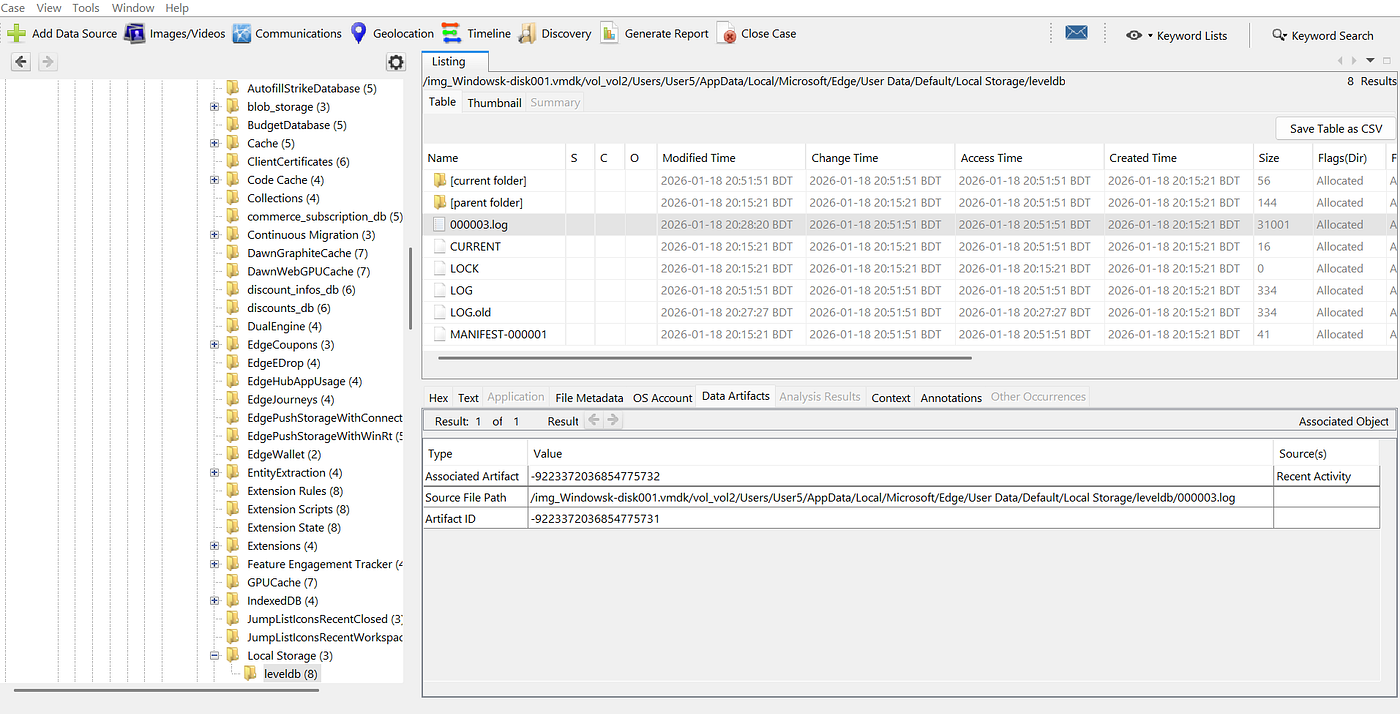
Using strings plus filtering around instructor, I recovered session-linked credential text.
SessionTokenT4r3Qhas5gfUserRoleinstructorFlag: KCTF{T4r3Qhas5gf}
Challenge 7 - Illegal Access to Admin3

Repeated BGInfo artifacts stood out during timeline and keyword review. I searched for bginfo globally in Autopsy and found a suspicious bitmap.
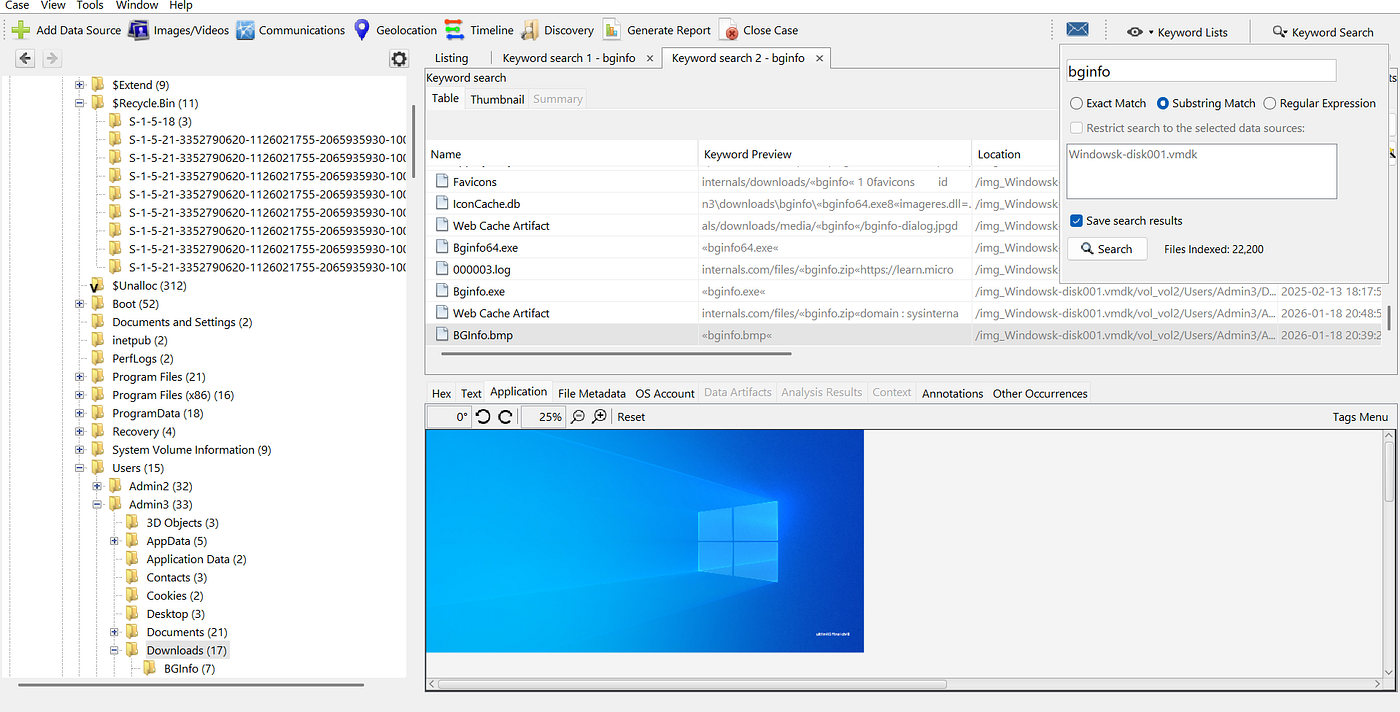
Zooming into the embedded white text revealed the final value.
Flag: KCTF{ult1m4t3_f1nal_ch4ll}
Closing Notes
This challenge set was a good mix of memory, filesystem, browser, and OS artifact analysis. The biggest lesson was to keep chaining clues from narrative context to technical evidence instead of treating each file in isolation.
Original publication: Medium post
